Set Up OneLogin SAML Custom Connector (Advanced) Application¶
Ensure that you have Administrator access to your OneLogin Account and Privacera.
Follow these steps to create and configure a OneLogin application for Single Sign-On (SSO) using a SAML Custom Connector (Advanced).
Step 1: Add a New Application¶
- Log in to your OneLogin Admin Console.
- From the top menu, select Applications and then click Add App.
- In the search bar, type "SAML Custom Connector (Advanced)" and select it from the results.
Step 2: Provide Basic Information¶
- In the Info tab, provide a descriptive name for your application in the Display Name field.
Example:Privacera SSO - OneLogin - (Optional) Upload a logo for the application if needed.
- Click Save to proceed to the next configuration step.
Step 3: Configure the SAML Settings¶
- Go to the Configuration tab.
- Fill in the following fields based on your SAML metadata information:
| Field | Value Example | Description |
|---|---|---|
| ACS (Consumer) URL | Self-Managed: https://PORTAL_HOST/saml/SSO PrivaceraCloud: https://privaceracloud.com/SingleSignOnService/receiveResponse | The Assertion Consumer Service (ACS) URL where SAML responses will be sent. |
| ACS (Consumer) URL Validator | Self-Managed: https://PORTAL_HOST/saml/SSO PrivaceraCloud: https://privaceracloud.com/SingleSignOnService/receiveResponse | A regex pattern that matches your ACS URL for validation. |
| Login URL | https://privaceracloud.com/login.html | The URL for login initiation. |
| SAML Audience | privacera_portal | Entity ID for SAML configuration. |
Step 4: Configure Parameters (Attribute Mapping)¶
- Go to the Parameters tab.
- Click + Add Parameter and add the following attributes to map user data:
| Field Name | Value to Send | Include in SAML Assertion | Sample Value | Description |
|---|---|---|---|---|
UserId | UserName | ✔ | UserName | Sends the user’s unique identifier. |
Email | Email | ✔ | Email | Sends the user’s email address. |
FirstName | FirstName | ✔ | FirstName | Sends the user's first name. |
LastName | LastName | ✔ | LastName | Sends the user's last name. |
memberOfGroupNames | User Roles | ✔ | User Roles (Semicolon Delimited input ) | This is an optional attribute that sends the list of groups the user belongs to. Select the checkbox for multi-value parameters |
- For each parameter, ensure you select the checkbox for Include in SAML assertion.
- For the
memberOfGroupNamesparameter, in addition to selecting Include in SAML assertion, also select the checkbox for Multi-value parameter to support multiple groups. - Click Save to proceed.
Step 5: Assign Users to the Application¶
- Go to the Users tab.
- Click + Assign and select Users or Groups.
- Choose the users or groups you want to assign and click Save.
Important
Ensure users are already mapped to the appropriate groups in One Login before assigning them to the application.
Step 6: Obtain the SAML Metadata¶
- In the SSO tab, locate the Issuer URL and SAML 2.0 Endpoint (HTTP).
- Copy both URLs for later use in the Privacera Portal.
Step 7: Review Your Configuration¶
- Review all the entered information and confirm that it is accurate.
- Click on the Save button.
You have successfully set up a SAML Custom Connector (Advanced) in OneLogin. This configuration is now ready to be integrated with Privacera Portal for Single Sign-On (SSO).
Configure OneLogin in your Privacera Account.¶
The steps to configure OneLogin integration in the Privacera Self-Managed (Portal).
Step 1: SSH into Privacera Instance¶
SSH into the instance where Privacera is installed.
Step 2: Navigate to Privacera Manager Directory¶
| Bash | |
|---|---|
Step 3: Copy the saml Sample Configuration File¶
Copy the sample saml configuration file to the custom configuration directory.
| Bash | |
|---|---|
Step 4: Rename the downloaded metadata XML file from OneLogin¶
- Locate the metadata file downloaded in Step 6, (usually in your
Downloadsfolder or the folder where you saved it). - Rename the file to
privacera-portal-aad-saml.xml
Step 5: Upload or Copy the File to Privacera Manager’s custom properties folder¶
Option 1: Using SCP (for Remote Servers)¶
- Open a terminal and run the following command to upload the file to the Privacera Manager’s custom properties folder: Replace
Bash <server-ip>with your server’s IP address anduserwith your username.
Option 2: Copy-Paste Locally¶
-
If the file is on the same server, move the
privacera-portal-aad-saml.xmlfile to the home directory. -
Use the following command to copy it to the custom properties folder
Ensure theBash privacera-portal-aad-saml.xmlfile is in the correct directory before running thecpcommand.
Step 6: Edit the Configuration File¶
Open the configuration file using a text editor and update the required fields.
| Bash | |
|---|---|
Uncomment and edit the following properties:
If you have configured Group Attribute, uncomment and edit the following properties:
| YAML | |
|---|---|
Step 7: Update Privacera Manager¶
Step 8: Optional - Role Mapping For One Login¶
Role mapping allows you to translate roles or groups from your OneLogin Identity Provider (IdP) into specific roles within Privacera. This ensures that users have the correct permissions and access when they log into Privacera.
What is Role Name Attributes?¶
This attribute in your IdP contains the user's roles or group information. It is used to identify the roles or groups the user belongs to in the IdP.
What is Role Mapping?¶
This configuration maps Identity Provider roles/groups to Privacera Portal roles. Matching roles are assigned to users; otherwise, The default role configured in the property (PORTAL_SSO_DEFAULT_USER_ROLE) from Privacera Manager is applied, Or ROLE_USER if unspecified.
Tip
Assign OneLogin Identity Provider (IdP) roles or groups for the Privacera Portal roles.
In Privacera, follow these steps to access the SAML Role mapping settings:
- Go to the Settings menu.
- Navigate to SSO Role Mapping.
- Click on SAML tab.
Reference image of Role Mapping form Privacera: 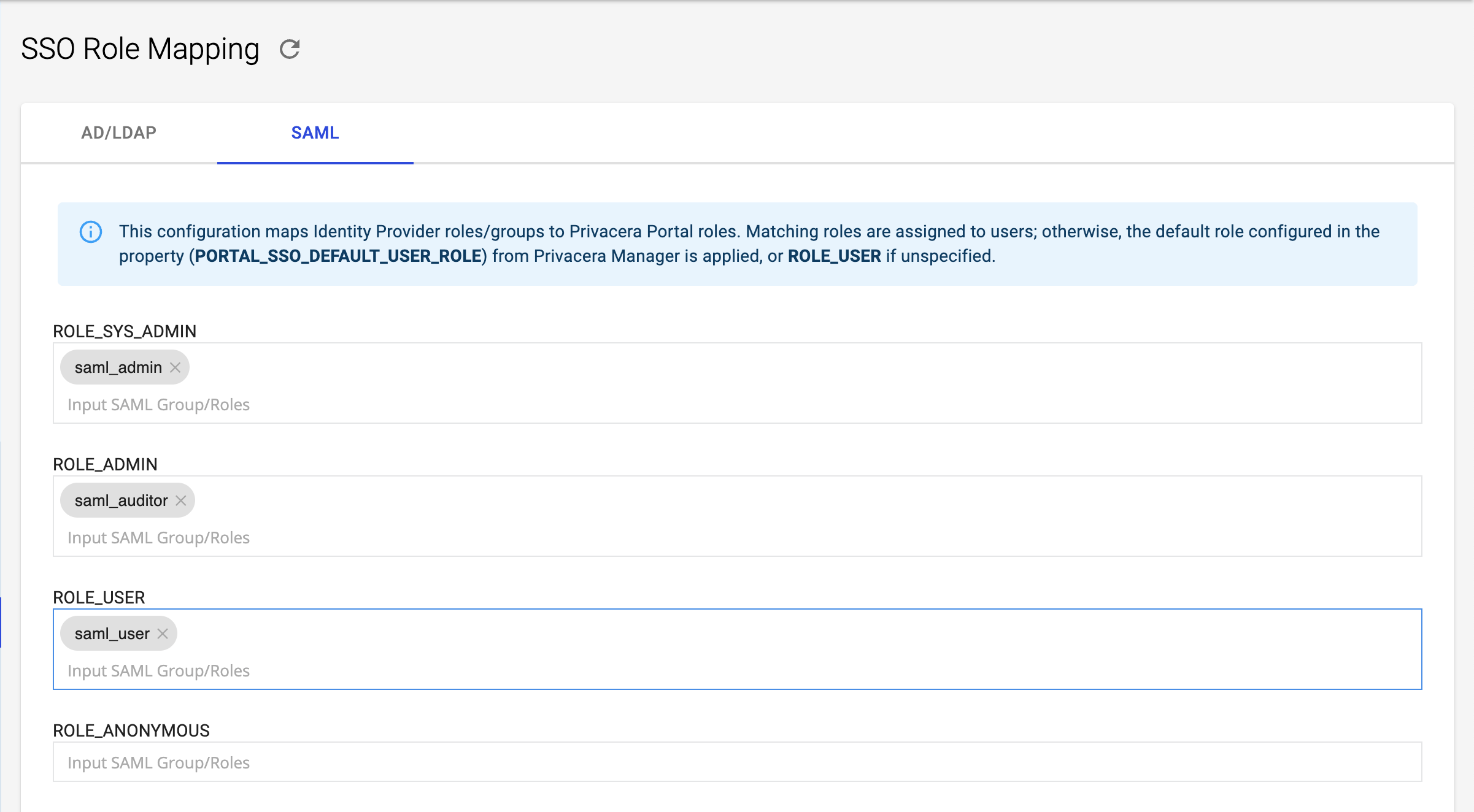
Example:¶
- Mapped Privacera Role:
ROLE_SYS_ADMIN - Identity Provider (IdP) Role or Group:
saml_admin
In this example, if a user has the role saml_admin in OneLogin, they will automatically be assigned the ROLE_SYS_ADMIN role in Privacera.
Step 9: Verify SSO Login¶
Once the setup is complete, navigate to the Privacera Portal login page. You should see an SSO Login button. Use this to log in with your OneLogin credentials.
In Privacera, follow these steps to access the Single Sign-On settings:
- Go to the Settings menu.
- Navigate to Identity.
- Click on Single Sign-On.
Reference image from PrivaceraCloud for better guidance: 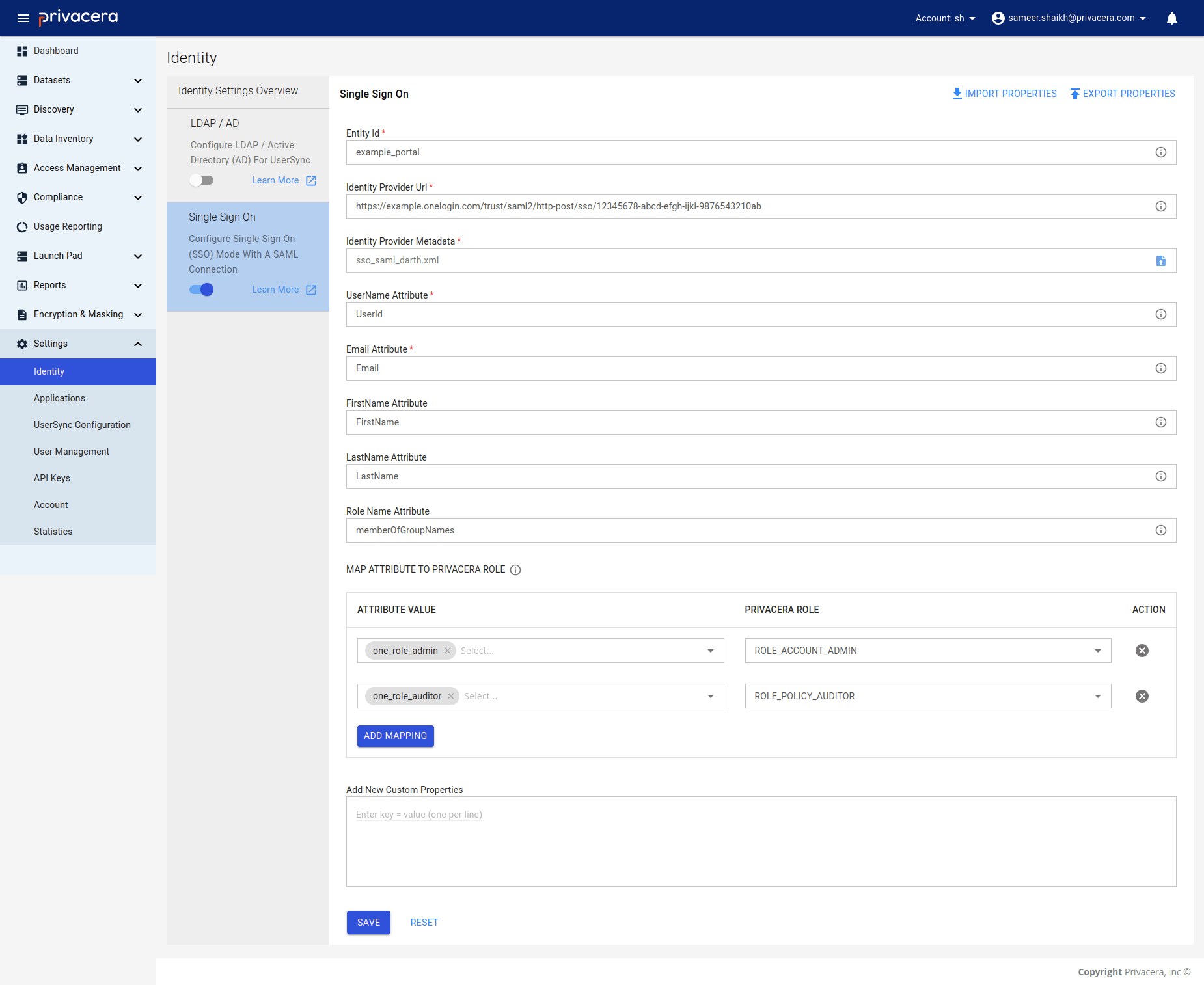
| Display Name | Description | Example Value | Optional/Required |
|---|---|---|---|
Entity Id | Entity ID for SAML configuration | privacera_portal | Required |
Identity Provider Url | Identity Provider URL | https://example.onelogin.com/trust/saml2/http-post/sso/12345678-abcd-efgh-ijkl-9876543210ab | Required |
Identity Provider Metadata | Metadata (XML file) | sso_saml_darth.xml | Required |
UserId | UserName attribute for SAML user | UserName | Required |
Email | Email attribute for SAML user | Email | Required |
FirstName | FirstName attribute for SAML user | FirstName | Optional |
LastName | LastName attribute for SAML user | LastName | Optional |
Important
- Entity ID: Used to configure the Identity Provider (IdP).
- Identity Provider URL: URL obtained in Step 6, where users will be redirected for SSO login.
- Identity Provider Metadata: Use the Metadata XML file downloaded in Step 6 for seamless SSO configuration.
- User Attributes: Ensure that the correct user attributes (
UserId,Email,FirstName,LastName) are mapped from OneLogin to Privacera.
These variables ensure seamless integration between oneLogin and Privacera for SAML-SSO.
Role Mapping For OneLogin¶
Role mapping allows you to translate roles or groups from your OneLogin Identity Provider (IdP) into specific roles within Privacera. This ensures that users have the correct permissions and access when they log into Privacera.
What is Role Name Attributes?¶
This attribute in your Identity Provider (IdP) contains the user's roles or group information. It identifies the roles or groups the user belongs to in the IdP.
What is Role Mapping?¶
This configuration maps roles or groups from the Identity Provider (IdP) to corresponding roles in Privacera.If a specific role from the Identity Provider (IdP) matches a role defined in the role mapping configuration, that role is assigned to the user in Privacera. If no mapping is defined, the default role, ROLE_USER, is automatically assigned to the user.
| Variable Name | Description | Example |
|---|---|---|
Role Name Attribute | Role name attributes for user. | memberOfGroupNames |
Role Mapping | Role mapping for user. | Identity Provider (IdP) Role: example_role → Example Role: ACCOUNT_ROLE |
Reference image of Role Mapping form PrivaceraCloud: 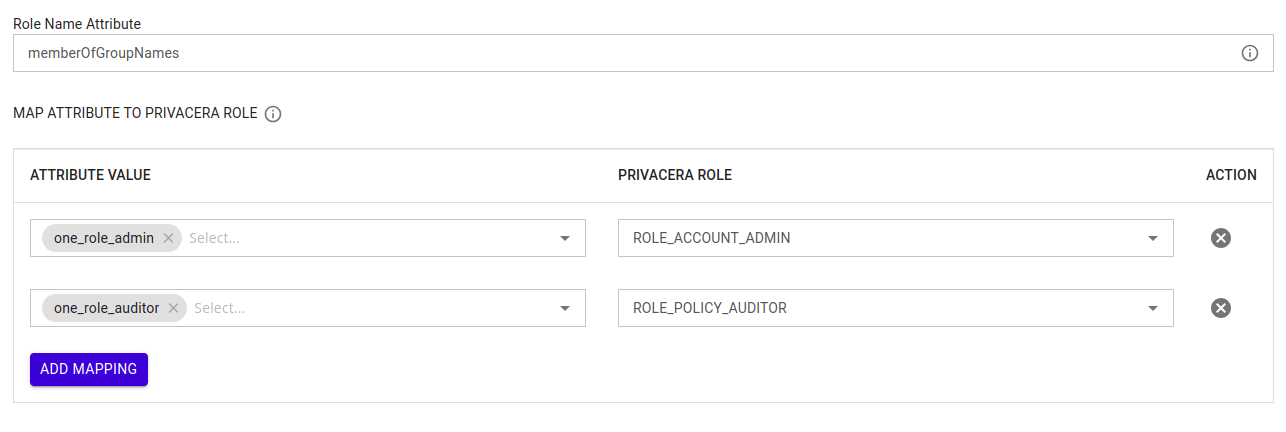
Example:¶
- Identity Provider (IdP) Role or Group:
one_role_admin - Mapped Privacera Role:
ACCOUNT_ADMIN
In this example, if a user has the role one_role_admin in OneLogin, they will automatically be assigned the ACCOUNT_ADMIN role in Privacera.
Important
New Users:
Role mapping only applies to newly created users after the mapping has been configured.
By properly configuring role mapping, you ensure that users are granted appropriate access levels within Privacera based on their roles or group memberships from the Identity Provider (IdP). This simplifies user management and ensures seamless integration with your organization’s existing identity infrastructure.
Once the configuration is complete, you can test the setup by attempting to log in to PrivaceraCloud using your OneLogin credentials. This will help verify that the Single Sign-On (SSO) integration is working correctly.